The MITRE Cybersecurity Incident🛡️🚨🕵️
A Look into Nation-State Exploits and Strategic Defense Mechanisms
MITRE, an organization well-known for its cybersecurity frameworks and standards, has experienced a significant compromise in their unclassified R&D network. This breach was reportedly conducted by a foreign nation-state threat actor who exploited vulnerabilities in an Ivanti Connect Secure appliance. The intruders leveraged this initial foothold, gained as early as January, to move laterally into MITRE's VMware infrastructure. This incident was brought to light by MITRE's CTO, Charles Clancy, who highlighted the incident in the context of promoting transparency and sharing their experience with the broader cybersecurity community.
The vulnerabilities that the attackers exploited included CVE-2023-46805 and CVE-2024-21887, as well as subsequent additional vulnerabilities such as CVE-2024-21893, CVE-2024-22024, and CVE-2024-21888. These vulnerabilities enabled a range of malicious activities from bypassing authentication, accessing restricted resources, privilege escalation, to potentially allowing a full domain compromise.
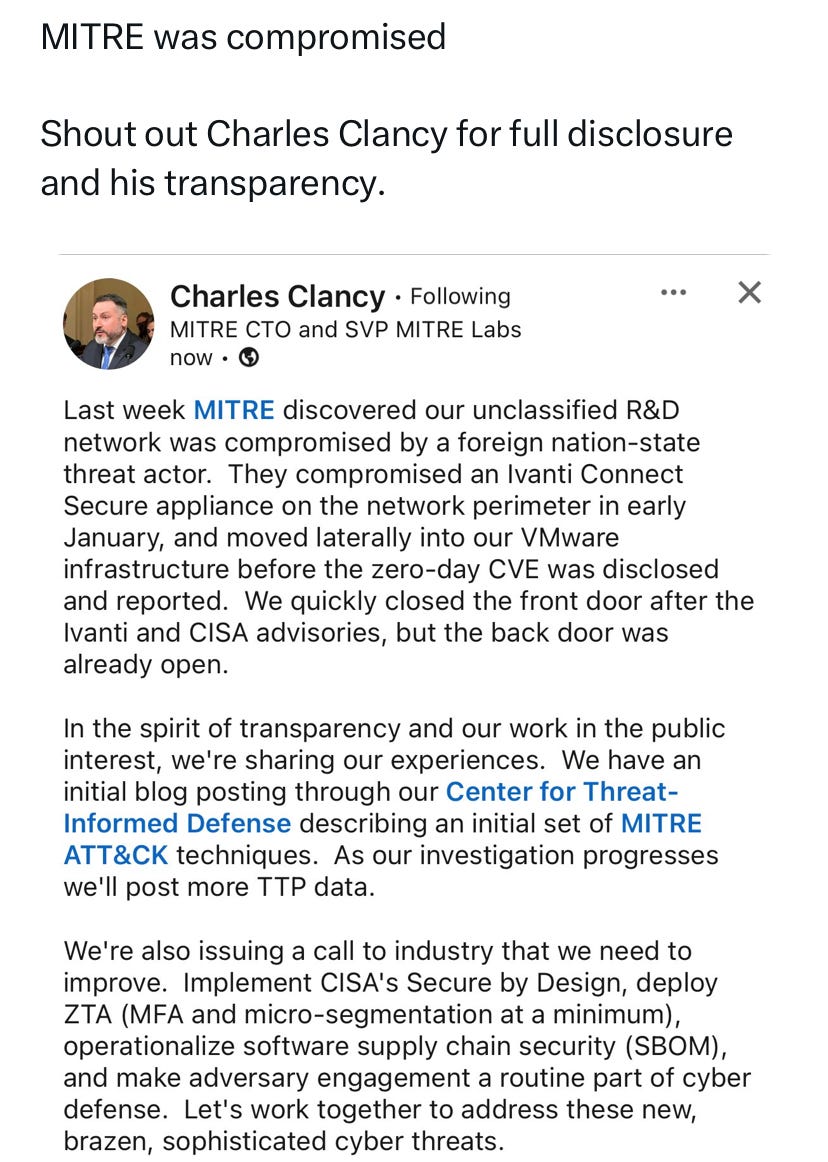
MITRE's response included an immediate implementation of initial mitigations advised by Ivanti and CISA (the Cybersecurity and Infrastructure Security Agency). However, the attack's complexity was significant as threat actors were able to bypass these initial mitigations, implanting various web shells for persistent access and control over compromised systems.
This breach is part of a larger pattern of exploitation against Ivanti vulnerabilities, which have seen widespread exploitation by various threat actors, leading CISA to issue an emergency directive for all civilian federal agencies to address these vulnerabilities. The directive requires immediate patching or mitigation efforts and highlights the unacceptable risk posed by these vulnerabilities to the federal enterprise. Agencies have been advised to assume full administrative access by threat actors and take comprehensive measures, including reimaging of compromised hosts and resetting of credentials.
In response to this wave of attacks, CISA, along with the FBI and international partners, has released a joint advisory providing detailed guidance on detection methods, indicators of compromise, and recommended actions and mitigations. The advisory stresses the importance of adopting secure-by-design principles and the implementation of effective cybersecurity controls to improve resilience against such sophisticated threats.
These events underscore the persistent and sophisticated nature of nation-state cyber threats and the importance of a proactive and transparent approach to cybersecurity. Organizations are urged to review and implement the recommended actions and mitigations to protect their systems and data from such vulnerabilities.

Objective:
To equip readers with the ability to identify and analyze the strategic motivations behind cyber attacks and to implement a proactive cybersecurity posture based on the principle of ‘assume breach’.
Why? Understanding the underlying motivations behind a cyber attack is crucial for developing a robust defense strategy and fostering a culture of resilience. In the case of MITRE’s breach, the motive appears to be espionage, a common goal for nation-state actors seeking to exploit intellectual property and strategic information. This scenario emphasizes the necessity for organizations, especially those handling sensitive data, to adopt a mindset of 'assume breach' and implement continuous monitoring and defense strategies to counteract sophisticated threats.
The concept of ‘nation-state cyber threat’ and its implications on global cybersecurity.
A 'nation-state cyber threat' refers to cyber attacks orchestrated by or on behalf of a country's government to pursue national objectives. These attackers are often part of or backed by the government's intelligence or military branches, equipped with substantial resources and advanced capabilities. The primary goals can range from espionage and intellectual property theft to disrupting critical infrastructure or influencing foreign political outcomes.
Implications on Global Cybersecurity:
Elevation of Cyber Defense Priorities: Nation-state attacks raise the stakes for national security, prompting countries to bolster their cyber defenses and develop offensive cyber capabilities as a form of deterrence.
International Norms and Regulations: These threats drive international discussions on establishing norms and rules of engagement in cyberspace, although achieving global consensus remains challenging due to differing national interests and governance models.
Escalation of Cyber Arms Race: As countries ramp up their cyber capabilities, there's an ongoing arms race in cyberspace, leading to an increase in the development and hoarding of cyber weapons. This situation can lead to more sophisticated and frequent cyber attacks globally.
Critical Infrastructure Risk: Nation-state actors often target critical infrastructure sectors (energy, water, finance) to cause disruption and panic or gain strategic advantages, underscoring the need for robust security in these essential services.
Economic and Political Impact: Cyber espionage and intellectual property theft by nation-states can have significant economic impacts, eroding competitive advantages of companies and economies. Moreover, meddling in elections or political processes of other countries can destabilize regions and skew diplomatic relations.
In addressing nation-state cyber threats, it's paramount for nations and organizations to adopt a proactive and resilient approach to cybersecurity. This means not only defending against attacks but also preparing to withstand and quickly recover from them. Collaboration among international bodies, governments, and the private sector is crucial to sharing intelligence, best practices, and strengthening collective defense mechanisms. The continuous evolution of cyber defense strategies, aligned with a clear understanding of the geopolitical landscape and emerging technologies, is essential in staying ahead of sophisticated nation-state actors.
The ‘assume breach’ philosophy and its importance in cybersecurity strategy planning.
The "assume breach" philosophy in cybersecurity is a strategic approach that operates under the assumption that an organization's defenses have already been, or will inevitably be, breached. This mindset shifts the focus from solely trying to prevent intrusions to also preparing robust mechanisms to detect, respond to, and recover from attacks effectively.
Embracing an "assume breach" philosophy is not about accepting defeat but about being prepared and vigilant. It's a call to action for organizations to fortify their cybersecurity defenses and cultivate a proactive security posture. This approach aligns with the reality of today's digital landscape, where the sophistication and frequency of cyber threats make breaches a matter of "when," not "if." It ensures that organizations are better equipped to handle and recover from incidents, ultimately safeguarding their assets, reputation, and trustworthiness in the long run.
Importance in Cybersecurity Strategy Planning:
Enhanced Detection and Response: By assuming that a breach will occur, organizations are compelled to develop stronger detection and response strategies. This involves investing in advanced monitoring tools, anomaly detection, and the integration of automated response systems to mitigate threats quickly and efficiently.
Resilience Building: Adopting an assume breach philosophy encourages the development of resilient systems and business processes that can maintain critical functions even when certain components are compromised. It prompts the implementation of redundancy, fault tolerance, and disaster recovery plans that ensure business continuity.
In-depth Defense Layers: This approach reinforces the concept of defense in depth—layering security measures so that if one fails, others still provide protection. It encourages the segmentation of networks, strict access controls, and the principle of least privilege, all of which help contain and limit the damage of a breach.
Regular Testing and Updates: Operating under the assumption of compromise, organizations are more likely to engage in regular testing and updating of their security systems. This includes frequent security audits, penetration testing, and the continuous assessment of security policies and procedures to identify and rectify vulnerabilities.
Culture of Security Awareness: The assume breach approach fosters a culture of security awareness among all employees. It stresses the importance of security best practices, such as being wary of phishing attacks and managing personal and sensitive data responsibly.
The characteristics of nation-state cyber actors and differentiate them from other types of cyber threats.
The attackers in this incident are described as nation-state actors, indicating that the breach was orchestrated by individuals operating under the auspices of a sovereign government. This aligns with a broader pattern of sophisticated cyber operations conducted by state-sponsored groups who possess advanced capabilities and are persistent in their efforts.
Nation-state cyber actors are distinct in their objectives, capabilities, and the persistence of their campaigns compared to other cyber threats like cybercriminals or hacktivists. These actors are often part of a government's intelligence, military, or contracted groups, operating with the full backing and resources of their state. Their primary aim is strategic; they seek to gather intelligence, influence geopolitical events, steal intellectual property, or disrupt critical infrastructure that could give their home country a political, military, or economic advantage.
In terms of capabilities, nation-state actors possess sophisticated tools and techniques, often developed or acquired at great expense. They are known for their ability to discover and exploit zero-day vulnerabilities—previously unknown software flaws—and for crafting advanced malware that often remains undetected for long periods. These actors employ multi-layered attacks that are meticulously planned and can span years, demonstrating a level of patience and resources not typically seen in other cyber threats.
Comparatively, cybercriminals are primarily motivated by financial gain. They tend to use more opportunistic attack vectors, targeting the lowest-hanging fruit unless a specific high-value target can be lucratively exploited. Cybercriminal activities often include ransomware attacks, credit card theft, and phishing schemes that are generally shorter-term in nature. On the other hand, hacktivists are motivated by ideological goals, seeking to make a statement or influence public opinion. Their attacks, such as website defacement or DDoS attacks, are usually aimed at drawing attention rather than stealth or long-term access.
The differentiation lies heavily in the combination of sophisticated capability, strategic intent, and the backing of a nation-state that sets these actors apart from other threats in the cyber landscape. Understanding these distinctions is crucial for tailoring defense strategies effectively against the specific types of threats an organization or nation may face.
Analyzing the role of software vulnerabilities in cybersecurity breaches and the importance of timely patch management.
In the cybersecurity breach involving MITRE, the exploitation of software vulnerabilities played a pivotal role, illustrating a classic vector through which attackers gain unauthorized access to secure systems. The vulnerabilities in question were found in Ivanti Connect Secure appliances, a key component used for secure connections to networks.
Specifically, the exploited vulnerabilities included CVE-2023-46805 and others in the 2024 series, which allowed attackers to bypass authentication, access restricted resources, and escalate their privileges within the network. The exploited vulnerabilities included CVE-2023-46805, CVE-2024-21887, CVE-2024-21893, CVE-2024-22024, and CVE-2024-21888.

CVE-2023-46805 is an authentication bypass vulnerability in the web component of Ivanti ICS and Ivanti Policy Secure, which allowed remote attackers to access restricted resources by bypassing control checks.

CVE-2024-21887 involves a command injection vulnerability in the web components of Ivanti Connect Secure and Ivanti Policy Secure, permitting an authenticated administrator to execute arbitrary commands on the appliance.
CVE-2024-21888 is a privilege escalation vulnerability in the web component of Ivanti Connect Secure and Ivanti Policy Secure, allowing a user to elevate privileges to that of an administrator.
CVE-2024-21893 is a server-side request forgery vulnerability in the SAML component of Ivanti Connect Secure, Ivanti Policy Secure, and Ivanti Neurons for ZTA, enabling an attacker to access certain restricted resources without authentication.
CVE-2024-22024 was mentioned as part of the exploited vulnerabilities, but specific details about this CVE were not provided in the sources.
These vulnerabilities collectively facilitated a range of malicious activities, from bypassing authentication and accessing restricted resources to privilege escalation and potentially allowing full domain compromise. The exploitation of these vulnerabilities underscores the critical importance of timely vulnerability management and patching, especially in environments used by high-value targets like MITRE.
Timely Patch Management
Timely patch management is a critical component of effective cybersecurity practices, serving as a fundamental barrier against potential breaches. Its importance is underscored by the frequent emergence of new vulnerabilities and the rapid pace at which these vulnerabilities are exploited by malicious actors.
1. Prevention of Exploits: Most cyber attacks leverage known vulnerabilities in software, which could have been mitigated by available patches. Implementing patches as soon as they are released drastically reduces the window of opportunity for attackers to exploit these vulnerabilities. In the context of the MITRE incident, the delayed patching of vulnerabilities in the Ivanti Connect Secure appliances provided a gateway for the attackers to infiltrate the network.
2. Maintaining Compliance and Trust: Many regulatory frameworks require up-to-date patch management as part of compliance standards. Failure to adhere can not only result in legal and financial penalties but also damage trust with clients and partners. Organizations that stay on top of their patch management obligations demonstrate a commitment to security, thereby bolstering their reputation and maintaining customer trust.
3. Reducing Security Risks and Costs: Timely patch management helps in maintaining the integrity and security of IT environments, reducing the risks associated with data breaches and cyber attacks. The costs associated with managing a breach, including remediation efforts, legal fees, penalties, and loss of business, often far exceed the resources needed to establish and maintain an effective patch management process.
4. Enhancing System Stability and Performance: Patches often include improvements to the stability and performance of software and systems, in addition to security updates. Regularly updating systems can lead to improved functionality and efficiency, helping businesses stay competitive and resilient in a fast-paced technological landscape.
5. Adaptation to the Evolving Threat Landscape: The threat landscape is continuously evolving, with attackers constantly developing new methods to exploit vulnerabilities. A proactive patch management strategy ensures that an organization can quickly adapt to these changes, minimizing the potential impact of new threats.
The cyber attack on MITRE's systems began with an exploitation of vulnerabilities in the Ivanti Connect Secure appliance, a typical starting point for attackers to establish an initial foothold. The attackers then leveraged this access to move laterally within MITRE's network, particularly into their VMware infrastructure. This kind of lateral movement is a stealthy technique that allows attackers to explore and compromise additional systems unnoticed, usually aiming to escalate their privileges or access sensitive areas. Throughout this period, the attackers likely used sophisticated methods to remain undetected, such as masking their activities to blend in with normal traffic and possibly using encryption to obfuscate command and control traffic. The timeline from breach to detection highlights the need for constant vigilance and advanced detection capabilities that can identify subtle anomalies indicating unauthorized access.
The strategic selection of network segments by attackers in orchestrating a breach.
In orchestrating a breach, attackers strategically select network segments that offer the most value or weakest security. For instance, in the MITRE breach, the intruders targeted the unclassified R&D network—a segment likely chosen for its valuable intellectual property and perhaps lower security barriers compared to classified networks. This approach allows attackers to maximize their impact by gaining access to sensitive information while minimizing the likelihood of early detection. The choice of network segments often reflects a calculated assessment of potential rewards versus risks, demonstrating a methodical approach to bypassing security defenses.
Exploring the technical methods used by cyber attackers, including specific exploits and lateral movement strategies.
In the MITRE breach involving Ivanti vulnerabilities, the technical methods used by cyber attackers showcase a blend of sophistication and strategic exploitation. Here’s an overview:
Initial Foothold and Exploitation of Vulnerabilities: The attackers began by exploiting several vulnerabilities in the Ivanti Connect Secure appliance, such as CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893. These vulnerabilities were critical as they allowed the attackers to bypass authentication mechanisms and access restricted resources, setting the stage for further malicious activities.
Lateral Movement and Privilege Escalation: After gaining initial access, the attackers employed lateral movement techniques to navigate through MITRE’s network. This involved moving stealthily across different segments of the network to reach more sensitive areas, such as the VMware infrastructure. The use of such tactics is indicative of the attackers’ intent to extend their control and reach within the network while remaining undetected.
Persistence and Stealth Techniques: To maintain presence within the compromised network without being detected, the attackers likely used various methods to blend in with normal network activity. This could include the use of web shells planted within the network, allowing them continuous and stealthy access. These web shells would enable them to execute commands remotely, further exploiting the network over time.
Bypassing Security Measures: Despite MITRE implementing initial mitigations as advised by Ivanti and CISA, the attackers were able to develop workarounds to these security measures. This indicates a high level of adaptability and resourcefulness, characteristic of advanced persistent threats (APTs), which are often backed by nation-state actors.
The techniques used in the MITRE breach highlight the importance of robust, multi-layered security strategies that include not just preventive measures but also advanced detection and response capabilities to counteract the sophisticated tactics employed by such adept adversaries.
Examining organizational response strategies to cyber breaches, assessing their effectiveness and areas for improvement.
Examining organizational response strategies to cyber breaches involves understanding how companies detect, contain, and mitigate the impacts of a security incident. The effectiveness of these strategies can significantly influence the resilience of an organization against future attacks and its overall security posture.
Immediate Incident Response: Organizations typically initiate an incident response plan as soon as a breach is detected. This plan includes identifying the breach, containing the damage, and collecting data for forensic analysis. For instance, MITRE's response to the breach involved immediate implementation of initial mitigations as advised by Ivanti and the Cybersecurity and Infrastructure Security Agency (CISA). The effectiveness of this response hinges on how swiftly and comprehensively the organization can react to limit damage. A key area for improvement in many organizations is the speed of detection and containment, as delays can lead to more extensive damage and higher recovery costs.
Long-term Mitigation Measures: Beyond the immediate response, effective strategies involve a thorough analysis of the breach to understand how it happened and how similar incidents can be prevented. This often includes a review and strengthening of security protocols, additional training for staff, and the adoption of more robust cybersecurity technologies. Organizations may also need to update or patch their systems to close any exploited vulnerabilities. An area for improvement here could be in the continuous adaptation and updating of security measures to anticipate and counteract evolving cyber threats rather than merely reacting to them.
Communication and Transparency: A crucial aspect of handling a breach is communication. This involves notifying all affected stakeholders, including customers, partners, and regulators, about the nature of the breach, what has been affected, and what is being done in response. MITRE's CTO highlighted the breach in the interest of promoting transparency and sharing lessons learned with the broader community, which is a positive approach. However, many organizations struggle with communication during a crisis. Improving timely and clear communication can help in managing the reputational damage and maintaining trust.
Regular Security Audits and Compliance Checks: Effective response strategies also involve regular audits and compliance checks to ensure that all systems are up to par with current security standards. This helps in identifying potential vulnerabilities before they can be exploited by attackers. A potential area for improvement is the frequency and depth of these audits, as well as ensuring that they cover all new and emerging threats.
Collaboration and Sharing of Intelligence: Finally, collaborating with other organizations and sharing intelligence about threats can greatly enhance an organization's ability to respond to and mitigate cyber attacks. This collective security approach can provide insights and warning signs from similar incidents faced by others, thus preparing organizations better against potential threats.
Conclusion
In conclusion, while many organizations have robust response strategies, there is always room for improvement, especially in adapting to the rapidly changing cyber threat landscape. Continuous learning, adaptation, and proactive defense measures are essential to staying ahead of cyber adversaries. The MITRE incident illustrates the relentless nature of cyber threats and the layered defenses required to mitigate them. It serves as a stark reminder of the need for continuous vigilance, rapid response capabilities, and a collaborative approach to cybersecurity, sharing knowledge and strategies within the community to fortify defenses collectively. This approach not only helps in mitigating the effects of a breach but also in understanding the adversary’s tactics, techniques, and procedures (TTPs), crucial for preparing against future threats.
References:
[1] CVE-2023-46805 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-46805
[2] CVE-2024-21887 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-21887
[3] CVE-2024-21888 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-21888
[4] Threat Actors Exploit Multiple Vulnerabilities in Ivanti Connect ... https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-060b
[5] CVE-2024-21893 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-21893
[6] CVE-2024-22024 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-22024
[7] CVE-2024-0204 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-0204
[8] CVE-2024-20252 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-20252
[9] Ivanti warns of a new actively exploited zero-day - Security Affairs https://securityaffairs.com/158403/hacking/ivanti-actively-exploited-zero-day-cve-2024-21893.html
[10] MITRE says state hackers breached its network via Ivanti zero-days https://www.bleepingcomputer.com/news/security/mitre-says-state-hackers-breached-its-network-via-ivanti-zero-days/







