Mastering the Digital Universe: Secrets of Hardware, Software, Networking, and Security 💻🔐🌐
The core components of technology in a way you've never seen before. Look into the heart of digital mechanics and secure your future with the ultimate guide to Technology.
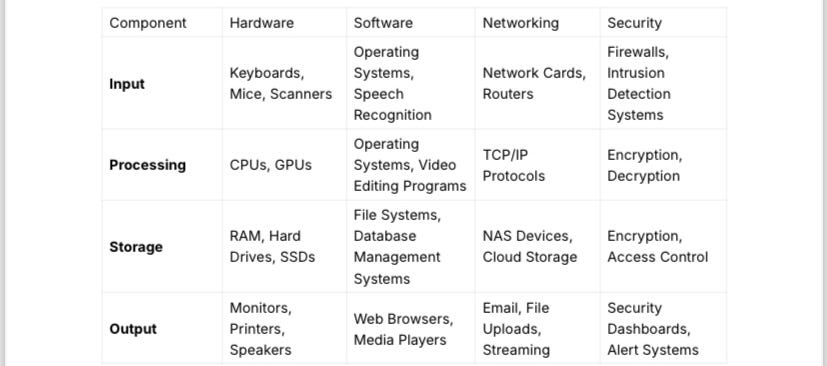
In technology, understanding the fundamental components of computing is crucial. The interplay between hardware, software, networking, and security forms the backbone of our digital world. This article provides a look into these elements, breaking down their roles in input, processing, storage, and output.
The Core of Computing: Hardware
Hardware is the tangible part of a computer system. It encompasses all the physical components that work together to perform computing tasks. Think of hardware as the skeleton and muscles of a digital body.
Input
Input devices are the tools that allow users to interact with a computer. These include keyboards, mice, scanners, and microphones. They convert physical actions into digital signals that the computer can process.
Example: When you type on a keyboard, each key press is converted into a digital signal that the computer's processor can interpret and act upon.
Processing
At the heart of any computer lies the Central Processing Unit (CPU). The CPU performs calculations and executes instructions, acting as the brain of the computer.
Example: When you run a program, the CPU processes the instructions in the software, performing billions of calculations per second to make the application work.
Storage
Storage devices retain data and programs. These can be volatile, like RAM (Random Access Memory), which temporarily holds data while the computer is on, or non-volatile, like hard drives and SSDs (Solid State Drives), which keep data even when the power is off.
Example: Your hard drive stores your operating system, applications, and files, while RAM holds data that the CPU needs quick access to, speeding up processing.
Output
Output devices display or produce the results of computer processing. Monitors, printers, and speakers are all output devices, transforming digital signals back into human-readable or perceptible forms.
Example: After processing your input, the computer sends the result to your monitor, allowing you to see your typed text on the screen.
The Soul of Computing: Software
Software is the intangible component that brings hardware to life. It consists of instructions that tell the hardware what to do. Without software, hardware would be a lifeless shell.
Input
Input software includes applications and systems that receive data from input devices. Operating systems (like Windows, macOS, and Linux) manage these inputs at a fundamental level.
Example: When you speak into a microphone, speech recognition software processes your voice into text or commands that the computer can execute.
Processing
Processing software includes operating systems, utilities, and applications that manage and perform tasks. This software orchestrates the actions of the hardware.
Example: A video editing program uses processing software to render video clips, apply effects, and combine audio tracks, leveraging the CPU and GPU for intensive tasks.
Storage
Storage management software ensures that data is saved and retrieved efficiently. File systems and database management systems fall into this category.
Example: When you save a document, the operating system’s file management software organizes the data on the hard drive, ensuring it can be quickly accessed later.
Output
Output software includes programs that present data to the user. Web browsers, media players, and graphic design software are all examples of output software.
Example: A web browser renders HTML code into visually appealing webpages, displaying text, images, and videos for the user to interact with.
The Backbone: Networking

Networking connects computers and devices, enabling communication and data sharing. It forms the infrastructure that allows the digital world to function cohesively.
Input
Networking input involves data received from other devices or the internet. Network cards, routers, and switches facilitate this data transfer.
Example: When you download a file, your network card receives data packets from the internet, which are then processed and stored by your computer.
Processing
Network processing includes protocols and software that manage data transmission and ensure accurate, efficient communication.
Example: TCP/IP protocols manage data packets traveling across the internet, ensuring they reach their destination correctly and efficiently.
Storage
Network storage involves data storage that is accessible over a network. Network Attached Storage (NAS) devices and cloud storage services fall into this category.
Example: Cloud services like Google Drive store your files on remote servers, allowing you to access them from any internet-connected device.
Output
Networking output involves data sent to other devices or the internet. This could be sending an email, uploading a file, or streaming a video.
Example: When you send an email, your computer processes the message and sends data packets through your network, eventually reaching the recipient's email server.
The Watch: Security

Security protects systems, networks, and data from unauthorized access and threats. It's the shield that safeguards the integrity and privacy of digital information.
Input
Security input involves monitoring and detecting potential threats. This includes firewalls, intrusion detection systems, and antivirus software.
Example: An antivirus program scans incoming files for malware, preventing harmful software from entering the system.
Processing
Security processing involves analyzing threats and responding to security incidents. This includes encryption, decryption, and the implementation of security protocols.
Example: When you access a secure website, SSL/TLS encryption ensures that the data exchanged between your browser and the server is secure from eavesdroppers.
Storage
Secure storage ensures that data is protected from unauthorized access. This includes encryption and access control mechanisms.
Example: Sensitive data, like credit card information, is often encrypted before being stored in databases, ensuring that even if the data is accessed, it cannot be read without the encryption key.
Output
Security output involves alerting users and administrators about potential threats and the status of security measures.
Example: A security dashboard provides real-time alerts and reports on attempted breaches, helping administrators take timely action to protect the system.
The Interconnected Digital World
Understanding how hardware, software, networking, and security interrelate is crucial for anyone navigating the digital landscape. Each component plays a vital role in the seamless operation of computer systems, from the initial input of data to the final output.
Hardware and Software Symbiosis
Hardware and software must work in harmony. Hardware provides the physical capabilities, while software directs these capabilities to perform complex tasks. This relationship is links to a body and mind working together to achieve a goal.
Networking as the Glue
Networking binds the disparate parts together. Without networking, computers would be isolated entities. Networking enables data exchange, collaboration, and access to a huge array of resources, making it the glue that holds the digital world together.
Security as the Protector
Security is the vigilant keeper. In a world where data breaches and cyberattacks are increasingly common, robust security measures are essential. They protect not just the data but also the trust users place in digital systems.
Conclusion: Embracing the Digital Future
To thrive in the digital age, one must grasp the intricate dance between hardware, software, networking, and security. Each component is a vital part of the larger system, contributing to the overall functionality and security of our digital lives.
By understanding these elements, you gain the wisdom to navigate the digital universe confidently, ensuring your systems are efficient, interconnected, and secure. As technology evolves, staying informed and adaptable will keep you ahead, ready to embrace new advancements and tackle emerging challenges.
In this interconnected digital world, mastering these components is not just beneficial—it's essential.