GuptiMiner: The Stealth of Cyber Threats🔣🔄⚠️
The importance of cybersecurity and the methods used by attackers to compromise systems.
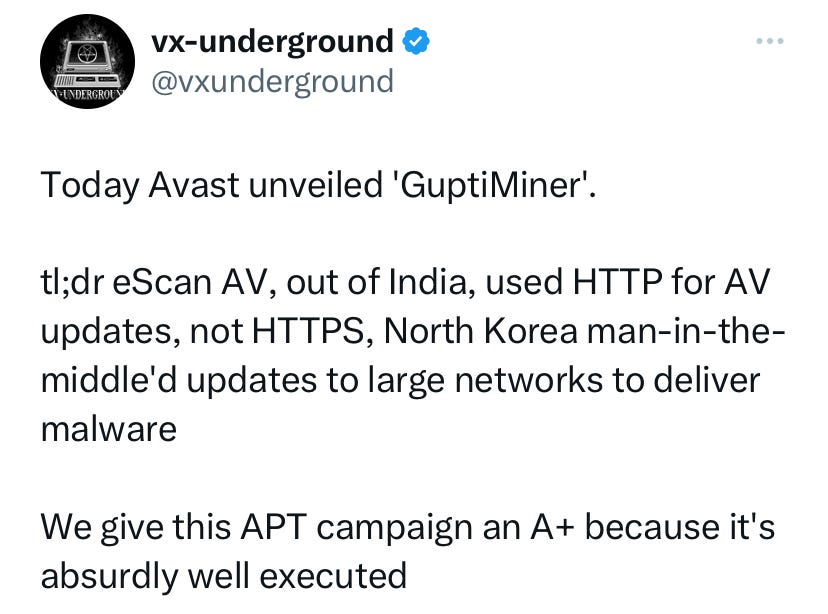
In cybersecurity, weaknesses in a system can be exploited to deliver malware through various attack methods. One such method is the 'man-in-the-middle' (MITM) approach, where an attacker intercepts and tamperers with communications between two parties, often to inject malicious code or steal sensitive information. In the case you mentioned, attackers exploited a weakness in the antivirus updates sent via HTTP, not the secure HTTPS, to infiltrate networks using an Advanced Persistent Threat (APT) campaign called 'GuptiMiner'. This campaign targeted large networks using eScan's antivirus updates, an antivirus company from India, and the attackers were linked to North Korea.
To understand the risks in cybersecurity, it is crucial to recognize that cybersecurity risk is the probability of exposure or loss resulting from a cyber attack or data breach on an organization. Cybersecurity risks relate to the loss of confidentiality, integrity, or availability of information, data, or information systems, reflecting potential adverse impacts on organizational operations, assets, individuals, other organizations, and the nation.
In the context of your query, the risks involved in the 'GuptiMiner' campaign include:
Exploitation of vulnerabilities: The attackers identified and exploited a weakness in the antivirus updates sent via HTTP, which should have been protected by the secure HTTPS protocol. This allowed them to intercept and tamper with the updates, potentially delivering malware to the targeted networks.
Advanced Persistent Threat (APT): The attackers used an APT campaign, which involves a long-term, targeted attack on a specific organization or network, often with the goal of stealing sensitive information or disrupting operations.
Nation-state involvement: The attackers were linked to North Korea, indicating that a foreign power was involved in the attack. This adds an additional layer of complexity and potential consequences, as nation-state attacks can have significant political and diplomatic implications.
The difference between HTTP and HTTPS.
HTTP (Hypertext Transfer Protocol) is the foundation of data communication on the web, but it's not secure. It's like sending a postcard; anyone who handles it can read it.
HTTPS (Hypertext Transfer Protocol Secure) is like sending a letter in a locked safe. It uses encryption (SSL/TLS) to keep the data safe from eavesdroppers.
Always look for HTTPS to keep your information secure online.
What is a man-in-the-middle attack?
A man-in-the-middle attack is like a sneaky eavesdropper. Someone secretly puts themselves between two parties talking to each other. Online, they can intercept, change, or steal the information being exchanged. Imagine you're passing a secret note to a friend, and someone else grabs it, reads it, and maybe even changes the message before passing it on. That's what happens in this kind of attack. Always verify who you're talking to online to avoid this.
Recognize the signs of an APT campaign.
An APT (Advanced Persistent Threat) is a stealthy threat actor, often a nation-state or state-sponsored group, which gains unauthorized access to a computer network and remains undetected for an extended period.
Signs of an APT campaign may include:
Unusual Outbound Data: Large amounts of data heading to unfamiliar locations.
Strange Account Behavior: Accounts acting oddly, especially at odd hours.
Unexpected Software: Programs you didn't install or that start on their own.
Security Alerts: Warnings from your security tools that are unusual.
Slow Network: Slower than usual performance, as if something is using resources.
If you notice these, take action. Secure your systems, and bring in experts if needed.
Empowerment comes from knowledge
Use HTTPS to safeguard data in transit, be vigilant for unusual system behavior indicating APT activity, and understand the methods attackers use to breach networks.
Resources
[1] What is Cybersecurity Risk? A Thorough Definition - UpGuard https://www.upguard.com/blog/cybersecurity-risk
[2] Cybersecurity Risk - Glossary | CSRC https://csrc.nist.gov/glossary/term/cybersecurity_risk
[3] What is Cyber Risk? Examples & Impact - Hyperproof https://hyperproof.io/resource/what-is-cyber-risk/ [4] Cybersecurity Threats: Types and Challenges - Exabeam https://www.exabeam.com/information-security/cyber-security-threat/
[5] [PDF] Man-in-the-Middle Attacks and “HTTPS Inspection Products” - HHS.gov https://www.hhs.gov/sites/default/files/april-2017-ocr-cyber-awareness-newsletter.pdf
[6] Top 15 Types of Cybersecurity Risks & How To Prevent Them - Executech https://www.executech.com/insights/top-15-types-of-cybersecurity-attacks-how-to-prevent-them/
[7] How to defend data from MITM attacks over HTTPS? - Stack Overflow https://stackoverflow.com/questions/11869036/how-to-defend-data-from-mitm-attacks-over-https
[8] Hackers infect users of antivirus service that delivered updates over HTTP | Ars Technica https://arstechnica.com/security/2024/04/hackers-infect-users-of-antivirus-service-that-delivered-updates-over-http/
[9] [PDF] Intelligence-Driven Computer Network Defense Informed by Analysis of ... https://www.lockheedmartin.com/content/dam/lockheed-martin/rms/documents/cyber/LM-White-Paper-Intel-Driven-Defense.pdf
[10] Hackers hijack antivirus updates to drop GuptiMiner malware - Bleeping Computer https://www.bleepingcomputer.com/news/security/hackers-hijack-antivirus-updates-to-drop-guptiminer-malware/
[11] Cybersecurity Risks | NIST https://www.nist.gov/itl/smallbusinesscyber/cybersecurity-basics/cybersecurity-risks
[12] Top 9 Cybersecurity Threats and Vulnerabilities - Compuquip https://www.compuquip.com/blog/cybersecurity-threats-vulnerabilities
[13] Malware vs. Exploits - Palo Alto Networks https://www.paloaltonetworks.com/cyberpedia/malware-vs-exploits
[14] Malware | BeyondTrust https://www.beyondtrust.com/resources/glossary/malware
[15] 13.3 Where Are Vulnerabilities? Understanding the Weaknesses https://open.lib.umn.edu/informationsystems/chapter/13-3-where-are-vulnerabilities-understanding-the-weaknesses/
[16] Know the types of cyber threats - Mass.govhttps://www.mass.gov/info-details/know-the-types-of-cyber-threats
[17] Advanced Persistent Threat (APT) Groups & Threat Actors - Mandiant https://www.mandiant.com/resources/insights/apt-groups
[18] Hackers Hijacking Antivirus Updates to Deliver GuptiMiner https://cybersecuritynews.com/antivirus-updates-hijacked/
[19] 2022 Top Routinely Exploited Vulnerabilities - CISA https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-215a
[20] An introduction to the cyber threat environment https://www.cyber.gc.ca/en/guidance/introduction-cyber-threat-environment






