Exploring the World of FIDO: Life Without Passwords 🗝️🚪🌐
Secure Keys, Web Wisdom, and Digital Doors
Secure Keys, Web Wisdom, and Digital Doors
In an era where the digital universe is expanding exponentially, the significance of cybersecurity can’t be overstated. Among the avant-garde of digital security lies the FIDO (Fast Identity Online) Alliance, an entity that’s reshaping the way we think about and implement cybersecurity. This article isn’t just a mere overview; it’s an expedition into the very heart of FIDO, decoding its various types, and the delicate dance of public and private keys.
Tech Talk | Coded Conversations | Substack
Unlock the secrets of cybersecurity with a twist - Coded Conversations 'Tech Talk' offers byte-sized, engaging insights…open.substack.com
Understanding the FIDO Alliance
At its core, the FIDO Alliance is a consortium aimed at revolutionizing the user authentication process. Formed in 2012, it’s a response to the growing need for stronger, simpler authentication methods beyond passwords. The alliance includes big names in technology and finance, all dedicated to creating authentication standards that are both secure and user-friendly.
Types of FIDO: SYM and ASYM Encryption
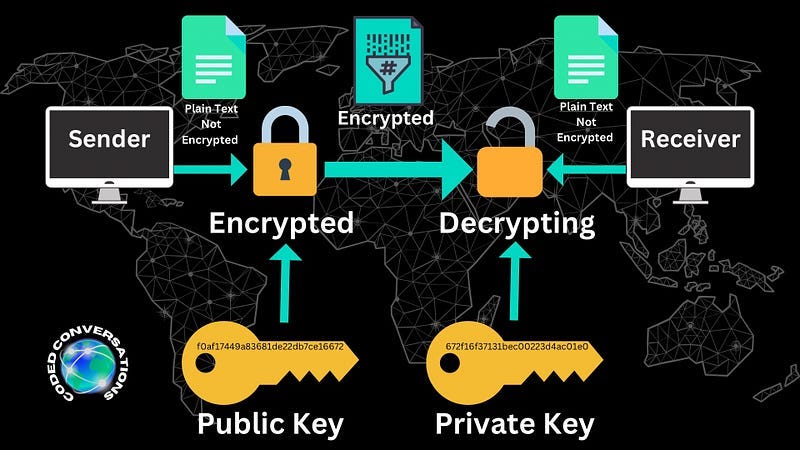
To grasp the essence of FIDO, one must first understand its two key types: SYM (Symmetric Encryption) and ASYM (Asymmetric Encryption).
SYM (Symmetric Authentication/Encryption): Imagine a secret handshake. In SYM, both the user and the server share a secret key for authentication. It’s akin to having a single key that both locks and unlocks a treasure chest. While simple and efficient, SYM has its drawbacks, particularly in key distribution and management.
ASYM (Asymmetric Authentication/Encryption): This involves two keys — a Public Key (PUB) and a Private Key (PVT). Think of it as a mailbox where anyone can drop a letter (encrypt data with the public key), but only the owner (who possesses the private key) can open it (decrypt the data).
Public and Private Keys: The Cornerstones of Digital Security
The Public and Private keys are central to the FIDO framework. The public key, as the name suggests, is openly available. It’s like your home address — everyone can know it, but they can’t enter your home. The private key, however, must remain confidential at all costs. It’s the key to your home, allowing you to access your secure digital space.
The Perils of Sharing Private Keys
Sharing a private key is like to giving someone unrestricted access to your most personal and sensitive digital assets. This not only compromises your security but also puts any data you’ve encrypted at risk. In a real-world scenario, consider the implications if a company’s private key were exposed. It would be a catastrophe, akin to leaving the vault door open in a bank.
Web Server Information and FIDO
When it comes to web servers, FIDO plays a critical role. A server, using FIDO protocols, can authenticate users without ever seeing or storing their private keys. This is revolutionary in reducing the risk of data breaches. Think of it like a bank that verifies your identity without ever needing to see your personal identification number (PIN).
The Evolution and Future of FIDO
The FIDO Alliance continues to evolve, addressing new cybersecurity challenges. Its latest advancements involve enhancements in biometric authentication and the development of FIDO2, which includes the WebAuthn standard, allowing users to log into their internet accounts with biometrics, mobile devices, or FIDO security keys.
Conclusion
The FIDO Alliance and its methodologies represent a paradigm shift in digital authentication. In this digital age, understanding and implementing robust cybersecurity practices like FIDO isn’t just advisable; it’s imperative. As we advance, FIDO’s role in securing our digital identities will only become more pivotal, making it a field worth watching and understanding. Let’s embrace this knowledge and step into a more secure digital future!
If you enjoyed this don’t forget to give a like, share with your peers, and leave your thoughts in the comments.
🔽 Read more about tech here: 🔽
@codedconversations | Linktree
Cybersecurity insights. No fluff all smarts. Learn easy, stay secure.linktr.ee
Cybersecurity Top World Headlines 📰🛡️
Top cybersecurity headlines from around the globemedium.com
Cybersecurity Role: Salary, Skills, and the Daily Grind 🔐 ⌛️⚙️
Salary, Skills, and the Daily Grind medium.com
Cybersecurity Meaning
An Insight into Cybersecurity’s Core Components and Noteworthy Incidentsmedium.com
Cybersecurity Quiz: Test Your Knowledge! 🛡️💻🔒
Instructions: Choose the best answer for each question. Good luck!medium.com
Cybersecurity: Bugs, Vulnerabilities, and Exploits
The Hierarchy of Digital Weaknesses and Threatsmedium.com